Miscellaneous
Machine Learning Resources
An Introduction to Statistical Learning, with Application in R Gareth James, Daniela Witten, Trevor Hastie, Robert Tibshirani This is a great book to start learning. It offers a gentle introduction to machine learning guided by examples. It gives little for granted and the mathematical notation is not heavy. It is beginner/medium level. With the “The Elements of Statistical Learning, Data Mining, Inference, and Prediction” offers a complete description of most well-known machine learning methods. It doesn’t discuss about neural networks. The Elements of Statistical Learning, Data Mining, Inference, and Prediction Trevor Hastie, Robert Tibshirani, Jerome Friedman It is the natural continuation of the “An Introduction to Statistical Learning, with Application in R” book. This book is medium/advanced level. It offers more in depth explanation where the introduction book hide some details. The mathematical is sometimes heavy. It does cover neural network in a chapter. Petter Recognition and Machine Learning Christopher M. Bishop This is the bible of all the machine learning books. It starts from the fundamentals to build up. It offers both frequentist and bayesian views of probabilities. The explanations are well discussed and easy to follow. Deep Learning Ian Goodfellow, Yoshua Bengio, and Aaron Courville The books talks about neural networks and most of its variants. It starts from the theory needed to understand all the concepts before diving into neural networks. Given the interest in this topic and the practical applications that use this methods worldwide, it is a book worth read it. Among other, it covers convolutional, recurrent and recursive neural networks.
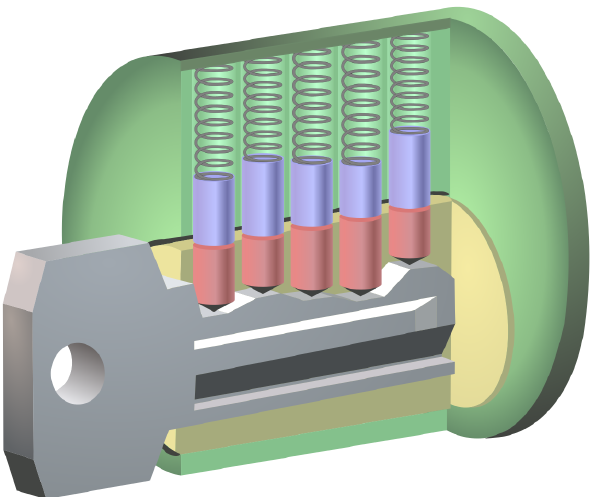
System Security Resources
This is a collection of system security resources that I found it interesting. Web Tangled Web, A Guide to Securing Modern Web Applications. Michal Zalewski A fantastic guide to understand the web and the browser. It starts from a historic view of the web and evolves to cover the modern world. Threat modeling Threat Modeling: Designing for Security Adam Shostack The Art of Software Security Assessment: Identifying and Preventing Software Vulnerabilities Mark Dowd, John McDonald, Justin Schuh Secure coding Secure Coding in C and C++ Robert C. Seacord A fantastic guide to really understand behind the hoods of a C/C++ program. It covers the explanations of different vulnerabilities but it does not guide you to exploit them. It covers the discussion on different coding standard, e.g., C99, OpenBSD and C11. One of the best book I have read. Exploitation Hacking, the Art of Exploitation Jon Erickson One of the bibles on exploitation. It covers shellcode, assembly, the exploitation of different vulnerabilities as well as some network and crypto attacks. Although the examples are mainly for 32 bit architecture, it is still a very good source of knowledge. The Shellcoder's Handbook: Discovering and Exploiting Security Holes Chris Anley, John Heasman, Felix Lindner, Gerardo Richarte -- Reverse engineering Practical Malware Analysis, The Hands-On Guide to Dissecting Malicious Software Michael Sikorski and Andrew Honig A good introduction -- Practical Binary Analysis, Build Your Own Linux Tools for Instrumenting, Analyzing, and Disassembling Binaries Dennis Andriesse It covers entirely the binary and its parts. It is a fairly new book and most of the examples are on 64 bit architecture. It covers also dynamic taint analysis and symbolic execution with practical tools. The IDA Pro Book, The Unofficial Guide to the World's Most Popular Disassembler Chris Eagle Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation Bruce Dang, Alexandre Gazet, Elias Bachaalany, Sébastien Josse Reversing: Secrets of Reverse Engineering Eldad Eilam
Web API Definition Guidelines
Web APIs are patterns of HTTP requests/responses used to interact with a remote system. APIs are meant to be used by programmers and for this reason they needs to be easy to understand and use as well as intuitive. Moreover, programmers will come with inherited knowledge base about what APIs looks like and what they do and they do not wants to learn a complete new language just for testing few new functionalities but they will most likely move to another technology that is more friendly and easy to use. REST vs RESTful? REST is the name given to the architectural pattern that defines means for clients and servers to exchange data. It is defined in a PhD disseration by Dr Roy Fielding in 2000 (but it is not a standard). As such, REST defines constraints on the elements of the architecture, for example: A REST application have a server that manages application data and state. The server communicates with a client that handles the user interactions (to change wording). servers don’t maintain any client state. Clients manage their application state. Their requests to servers contain all the information required to process them. (to change wording). (These are just 2 examples.) REST is the architectural pattern proper of HTTP. It was defined after the definition of HTTP that’s why the terms are misinterpreted to be the same. When we talk about RESTful we refer to services that are based on REST architecture style. RESTful is not clearly defined even if it uses defined standards such as HTTP, URI and JSON. Introduction In this article, I am trying to summarise the best practices that have been captured in two books by a leader player in this field: Web API Design Web API Design: The Missing Link Therefore I will make extensive use of their examples. We need to remember that REST APIs follow a data-oriented approach that focus on the objects they interact with (rather than the function to manipulate such objects). REST API focuses on the object they expose rather than the functions to manipulate the object. So for instance when you ask for an object you can refer to the objects as /objects (e.g., /dogs). In contrast you can have function-oriented API e.g., /getDogs. The link 0 When defining APIs, it’s always necessary to publish at least one well-known URL. This is the minimum amount of URL that a developer needs to know in order to get started. It should be possible to explore the APIs only by using this one URL. When you request a URL you will receive a representation of the resource requested. The most supported languages to represent a resource is JSON. If you request “https://dogtracker.com” you will receive it’s representation as: { "self": "https://dogtracker.com/", "kind": "DogTracker", "persons": "https://dogtracker.com/persons", "dogs": "https://dogtracker.com/dogs" } The representation contains a URL to itself and other URLs to other collections of objects (dogs and persons in this example). When querying a collection you can receive its representation as: { "self": "https://dogtracker.com/dogs", "kind": "Collection", "contents": [ { "self": "https://dogtracker.com/dogs/12344", "kind": "Dog", "name": "Fido", "furColor": "white" }, { "self": "https://dogtracker.com/dogs/12345", "kind": "Dog", "name": "Rover", "furColor": "brown" } ] } The list of objects inside of the “contents” its a mere list of the objects requested. It’s common to name a collection with the plural name of the requested objects. E.g.: the collection “dogs” represent the a collection of “dog” objects. To query a collection for a particular object, it is traditionally done following two different approaches: https://example.com/objects/{objectID} https://example.com/search?type=object&id={objectID} This structure enables a simple and intuitive tree navigation that expresses relations with other objects, e.g.: https://example.com/persons/12345/dogs/09876 Without saying anything this URL we are requesting the dog 09876 among the ones linked to person 12345. Furthermore, because many application developers consuming the API find the first style more readable and intuitive. API developers implementing the API usually find the first style easier to implement. For many people, the first style of query URL does not imply a commitment to a comprehensive query capability, but they are more likely to interpret the second style of query URL to mean that all combinations of query parameters and values are supported. This style of query URL can easily express graph traversal queries that are difficult to express in the query parameter style. Many times instead, it is difficult to request objects following a hierarchical structure. In that case you can use: https://example.com/persons/5678/dogs?color=red&state=running&location=park Identify a resource All resources needs to have a link that can be saved and stored by the client to be used later on therefore it must be as much stable as possible. For example, resources can be identified by human-friendly identifiers as: https://dogtracker.com/person/JoeMCarraclough It is clear that if the person requested change name (and therefore its URL) all the reference will break. Resources can be also identified by machine-generated identifiers: https://dogtracker.com/persons/e9cdcf7a-25b3-11e5-34363bd0ac10 In this case the URL is not human-friendly not ideal for developers. A good solution is to use machine generated URLs to identify a specific resource and give to that resource an alias property human-friendly that points to it. E.g.: { "self": "https://dogtracker.com/person/e9cdcf7a-25b3-11e5-34363bd0ac10", "id": "e9cdcf7a-25b3-11e5-34363bd0ac10", "kind": "Human", "name": "LasJoeMCarraclough", "alias": "https://dogtracker.com/persons/JoeMCarraclough", } When referring to this resource you have to use the permanent link, e.g.: { "id": "12345678", "kind": "Dog", "name": "Lassie", "furColor": "brown", "owner": "https://dogtracker.com/persons/e9cdcf7a-25b3-11e5-34363bd0ac10" } The permanent link to the person is https://dogtracker.com/persons/e9cdcf7a-25b3-11e5-34363bd0ac10. This link implies that the kind person cannot change. This is reasonable assumption for humans, but it might be not true for other entities. Resource fields A good example of resource is: { "self" : "https://dogtracker.com/persons/34363bd0ac10", "id" : "e9cdcf7a-25b3-11e5-34363bd0ac10", "kind" : "Human", "name" : "LasJoeMCarraclough", "alias" : "https://dogtracker.com/person/JoeMCarraclough", "dogs" : "https://dogtracker.com/persons/34363bd0ac10/dogs", "actions": "https://dogtracker.com/persons/34363bd0ac10/actions" } Including a kind property helps clients recognize whether or not this is an object they know how to process. Including a self property makes it explicit what web resource’s properties we are talking about without requiring contextual knowledge. E.g.: the resource can be retrieved by directly performing a GET request. Including a actions property is needed to modelling the action that the resource can perform. A POST request can be performed to request a specific action on a resource followed by the details of such action. It is possible also to specify the actions that can be performed to a resource with different fields, e.g.: { "pauseRequests": "https://dogtracker.com/persons/34363bd0ac10/actions", "stopRequests" : "https://dogtracker.com/persons/34363bd0ac10/actions" } Note that all the action fields point to the same URL. The name of the fields can follow either camelCase or snake_case equivalently but they need to be consistent. When an object representation contains too many fields it is possible to request only a subset of them as: Adding, removing, changing resource When you model your URIs after resources and use HTTP verbs you make your API predictable. Once developers know how you defined your resources, they can almost predict what the API looks like. In REST, adding a resource is usually expressed with a POST to the collection that have these objects, e.g.: POST https://dogtracker.com/persons/34363bd0ac10/dogs This request indicates the intention to add a dog to the person 34363bd0ac10. A GET request is used to express the intention of retrieving the resource details. A PUT request is used to completely replace the resource we are pointing. A PATCH request instead is used to alter the value of a particular field. What to do for versioning? We all understand that at some point in time, APIs will change. If you can change your API in a backward-compatible ways then this is the way to go. When changes are breaking the backward-compatibility then you might want to add a version in the requesting URL as: https://dogtracker.com/v2/persons/98765432 When requesting such URL, the representation returned can include the version as well: { "self" : "https://dogtracker.com/v2/persons/34363bd0ac10", "id" : "e9cdcf7a-25b3-11e5-34363bd0ac10", "kind" : "Human", ... Error handling An API is a shield that hide the computation performed behind it. Remember that programmers learn by trial and error, therefore the importance of messages is extremely valuable. For example, when a request is created the response can include the Location header to express where is it located, e.g. HTTP/1.1 201 Created Location: https://dogtracker.com/dogs/1234567 When a method is not permitted: HTTP/1.1 405 Method Not Allowed Allow: GET, DELETE, PATCH Learning the combinations of status codes with their matching headers and the scenarios in which they are used is important. A programmer can use her knowledge of the web to navigate throw the errors to succeed. Extreme summary * REST API focuses on objcets: nouns are good, verbs are bad * https://example.com/objects/{objectID} * https://example.com/objects?property1=value1&property2=value2 1. Nouns are good, verbs are bad This does not matter much because the details will be mostly used by automatic program that do not care about the format. For the query URLs instead the format should be easily human readable because they will be used by the developers. -- Additional Resources on REST https://www.ics.uci.edu/~fielding/pubs/dissertation/rest_arch_style.htm https://en.wikipedia.org/wiki/Representational_state_transfer https://blog.ndepend.com/rest-vs-restful/
CTF Resources
During the time I have collected various resources that help me practicing CTF skills, divided per each category. Some of the exercises found in these sites are solved in the Security Exercises section. Web Web https://github.com/cure53/XSSChallengeWiki/wiki The repo offer a good collection of XSS related challenges. Although last update is from 2014, it stores a lot of references to other websites with related solution. Web https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/XSS%20Injection The repo offers examples of XSS in different scenarios. Web https://github.com/s0md3v/AwesomeXSS The repo has good reference material to understand XSS and some references to existing challenges. Reverse Reverse https://challenges.re It offers many reverse challenges dividing them in categories as OS, architecture and levels. It does not provide solutions. Crypto Crypto https://cryptopals.com Very good reference to implementing algorithms. It goes from zero to hero. It helps you to build famous crypto attacks like breaking an MD4 and SHA-1 keyed MAC using length extension. It doesn't offer challenges like broken algorithms to brake or CTF like challenges. Exploit Exploit https://github.com/shellphish/how2heap It is a colletion curated from the Shellphish team from UCSB. Exploit http://pwnable.kr/play.php Very famous and well curated site that offers a good variety of challenges. There are a lot of online write ups if you are stuck. Exploit https://old.liveoverflow.com/binary_hacking/protostar/stack0.html A very good resource for stack-based and heap-based buffer overflow. The challenges were thought for 32 bit architecture and the the online videos as well but with provided the source code you can compile it in 64 bit as well. Exploit https://ropemporium.com The site offers many resources to guide you through the construction of ROP. It offers both 64 and 32 bit examples for the same challenge. Network Forensics -- Miscellaneous Write-up https://github.com/ctfs A collection of write ups from previous CTFs divided per year. CTFs Reference https://ctftime.org This is the place where you want to be to get news and upcoming events always up to date.